In the face of an ever-present and evolving digital threat landscape, cybersecurity has transformed from a technical necessity into a comprehensive B2B Cybersecurity Market Solution that addresses a wide spectrum of critical business problems. It is the fundamental solution to maintaining business continuity in an age where a single cyberattack can halt operations for days or weeks. The rise of ransomware, in particular, poses an existential threat. The problem is not just encrypted data; it is the complete shutdown of manufacturing lines, cancellation of hospital appointments, and disruption of critical supply chains. A multi-layered cybersecurity strategy provides the solution. This includes proactive measures like robust email security and employee training to prevent the initial infection, advanced Endpoint Detection and Response (EDR) to stop the malware's execution, and a defense-in-depth network architecture to prevent its lateral movement. Crucially, it also includes a resilient backup and recovery solution that ensures the business can restore its data and systems quickly without paying a ransom, transforming a potentially catastrophic event into a manageable incident and ensuring the organization's survival and continued operation in a hostile environment.
Another core business problem that a robust cybersecurity program solves is the protection of an organization's most valuable asset: its data. In the digital economy, businesses collect and generate vast amounts of sensitive information, including customer personal data, intellectual property, financial records, and strategic plans. The problem is that this data is a prime target for theft by cybercriminals looking for financial gain or state-sponsored actors seeking a competitive or strategic advantage. A successful data breach can lead to devastating consequences, including direct financial loss, erosion of customer trust, loss of competitive advantage, and severe regulatory penalties. A comprehensive B2B cybersecurity solution addresses this problem head-on. Data Loss Prevention (DLP) solutions monitor and control the flow of sensitive data to prevent its unauthorized exfiltration. Robust encryption, both for data at rest in databases and in transit across networks, makes stolen data unusable to attackers. Strong Identity and Access Management (IAM) and privileged access management (PAM) controls ensure that only authorized personnel can access sensitive information, mitigating the risk of both external attacks and malicious insiders.
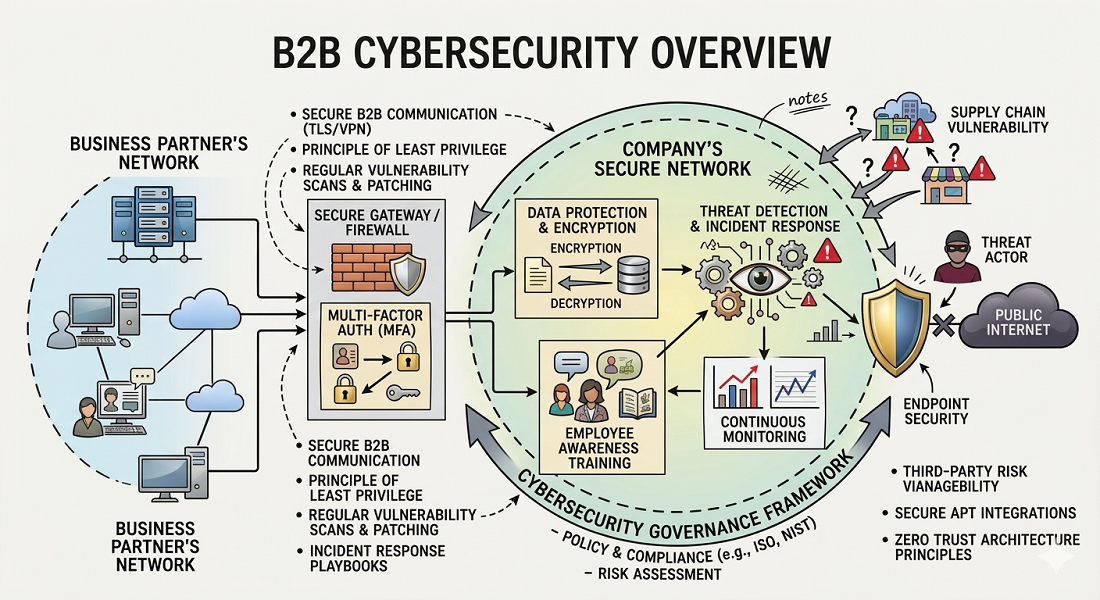
In today's globalized economy, businesses operate within a complex web of partners, suppliers, and customers. This interconnectedness creates immense value but also introduces a significant new problem: supply chain risk. An organization can have a perfect security posture, but it can still be compromised if one of its trusted software vendors or service providers is breached. High-profile incidents have shown that attackers are increasingly targeting the supply chain as a weak link to gain access to hundreds or thousands of downstream targets. The cybersecurity solution to this complex problem is multifaceted. It involves implementing rigorous third-party risk management (TPRM) programs to vet the security of all vendors and partners. It requires the use of Software Bill of Materials (SBOM) to gain visibility into the open-source components used in commercial software, allowing for rapid identification of vulnerable applications. It also involves adopting a "zero trust" architecture, which assumes that no part of the network—including traffic from trusted partners—is inherently safe, and therefore requires strict verification and segmentation to limit the potential blast radius of a supply chain compromise.
Finally, B2B cybersecurity is the essential solution to the complex and ever-growing problem of regulatory compliance. In virtually every jurisdiction and industry, businesses are now subject to a dense thicket of laws and regulations governing data privacy, security, and breach notification. The problem for businesses is that achieving and demonstrating compliance with these varied regulations (like GDPR, HIPAA, PCI DSS) is a daunting and resource-intensive task, with non-compliance carrying the risk of massive fines. A structured cybersecurity program provides the solution by implementing the very controls that these regulations demand. Security Information and Event Management (SIEM) systems provide the comprehensive logging and auditing capabilities required by many compliance frameworks. Vulnerability management programs systematically identify and remediate security flaws, a core requirement of standards like PCI DSS. Data classification and governance tools help organizations understand where their sensitive data resides, a prerequisite for complying with privacy laws like GDPR. By aligning security practices with compliance frameworks, cybersecurity programs not only reduce risk but also provide the evidence needed to satisfy auditors and avoid regulatory penalties, making it a critical solution for legal and financial risk management.
Explore Our Latest Trending Reports!